I say this as someone who has 70+ smart devices in my home: the default privacy settings on most smart home devices are bad, the data practices of major manufacturers are worse than most people realize, and "if you have nothing to hide" is not a reasonable response to a microphone sitting in your bedroom. Let me tell you what's actually happening and what you can do about it.
This isn't a conspiracy theory. It's documented behavior backed by privacy policies, security research, and enforcement actions from the FTC.
What Your Devices Are Actually Collecting
Smart speakers (Echo, Google Nest) are the obvious ones. They listen for wake words constantly. Amazon and Google both employ humans who review voice recordings to "improve" their AI. You can opt out, but the default is opt-in. Amazon's Alexa has been caught recording conversations after false wake-word triggers and storing them. This is documented, not speculation.
Smart TVs are data collection machines that happen to play video. Automatic Content Recognition (ACR) tracks every show you watch, every channel you surf, every ad you see — and sells that data to advertisers. Vizio paid a $2.2 million FTC settlement over exactly this. Samsung, LG, and Roku all have similar ACR programs enabled by default. Most smart home people forget their TV is a smart home device.
Robot vacuums map your home. That floor plan — the layout of your rooms, where your furniture is, how large your home is — goes to manufacturer servers. iRobot (Roomba) had a plan to sell home layout data before it became public and they walked it back under pressure. The data is still being collected. You just don't know what happens with it.
Doorbell cameras log every time someone approaches your house. Ring (Amazon) has shared footage with law enforcement without user consent or warrants in specific circumstances. The policy has changed but the capability remains. Eufy had footage accessible via unauthenticated streams despite claiming end-to-end encryption.
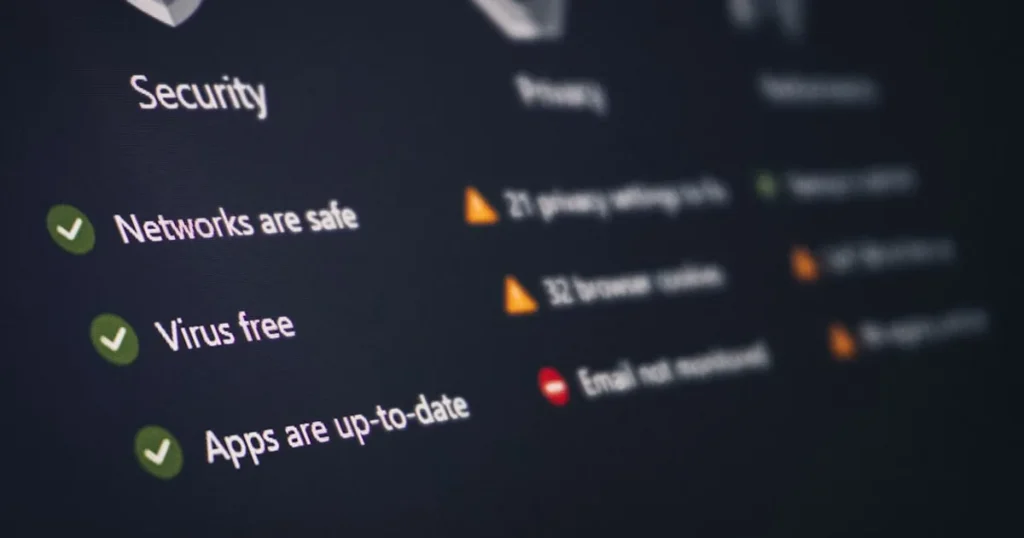
Smart light bulbs and plugs seem innocuous, but they log when you're home, when you're asleep, and your daily patterns. That information is on a company's server somewhere.
The Three Threat Models
Before you go paranoid, understand who you're actually protecting against.
Hackers and criminals want to use your smart home against you — camera feeds, door lock access, or your home network as an entry point to steal financial data. This is a real risk, especially with cheap unbranded devices.
Manufacturers and data brokers want behavioral data to sell to advertisers. This is the most common privacy issue. It's legal, happens constantly, and most people have consented to it without reading the terms.
Government and law enforcement can request data from manufacturers, sometimes without your knowledge. This is rare for normal people but worth understanding.
Most people should focus their energy on threat #1 (real security) and #2 (data collection), not #3. Unless you have specific reasons to worry about law enforcement, that's not your top priority.
Step One: Lock Down Your Network
Put your smart home devices on a separate Wi-Fi network (VLAN or guest network). Most modern routers support this — your Eero Pro 6E, Asus RT-AX88U, or Ubiquiti UniFi setup can all do it.
Here's the thing: if a cheap $8 smart plug gets compromised, it should not have access to your laptops, phones, and NAS drives. Network segmentation means a compromised device can communicate with the internet (so it still works) but can't access other devices on your main network. This takes 20 minutes to set up and meaningfully reduces your attack surface.
Block internet access for devices that don't need it. Most smart home sensors (motion sensors, contact sensors, temperature sensors) only need to talk to your local hub, not the internet. Block their outbound traffic at the router. A Zigbee sensor connected to Home Assistant doesn't need internet access at all.
Step Two: Change Default Passwords. Every Single Time.
A staggering percentage of smart home compromises happen because people leave default admin credentials on their devices and routers. The router your ISP gave you probably has default credentials like "admin/admin" that every script kiddie knows.
Change your router admin password. Change credentials on any camera with a web interface. Enable two-factor authentication on your Google, Amazon, and Apple accounts that control your smart home. These are boring basics that actually matter more than anything fancy.
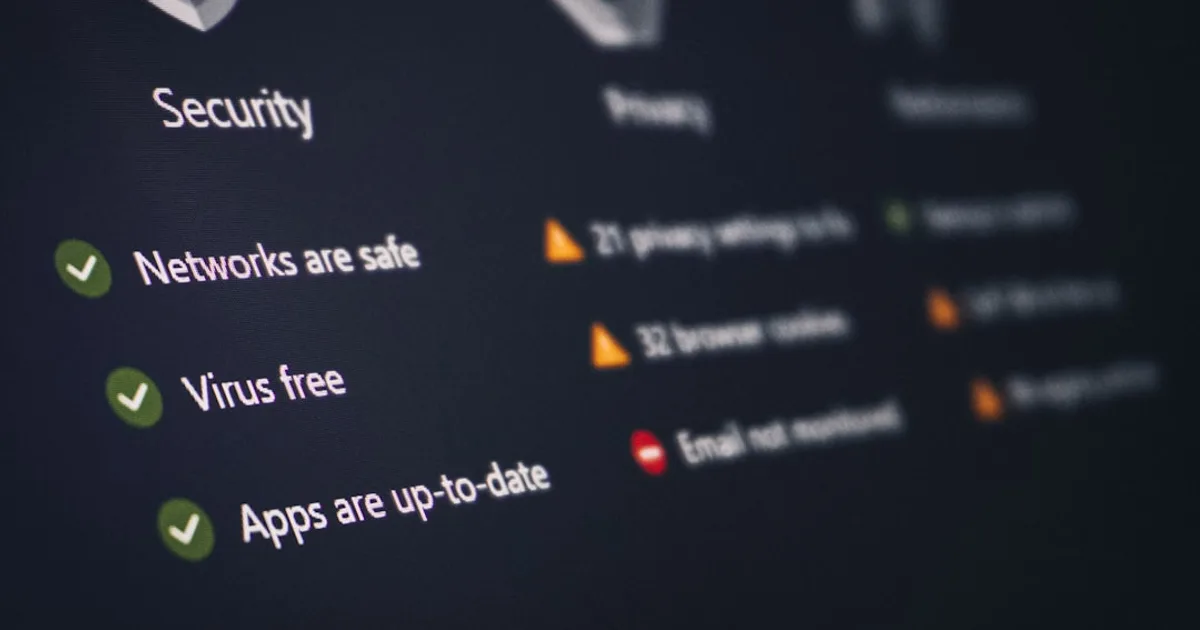
Step Three: Audit What's Actually Phoning Home
Pi-hole ($0, runs on a Raspberry Pi) is a DNS sinkhole that logs every DNS request your devices make. Set it up, wait a week, and see what your devices are contacting. I found that one of my smart TV brands was making 2,000+ requests per day to advertising servers. Some of those you can block at the Pi-hole level without breaking device functionality.
This is technical but not hard — the Pi-hole documentation is excellent and there are installers that take 15 minutes.
Step Four: Prefer Local Control
The most durable privacy solution is devices that don't require manufacturer cloud infrastructure. If data never leaves your home network, it can't be collected, breached, or subpoenaed.
Home Assistant is the platform that makes local control practical. Zigbee devices (Aqara, IKEA, Sonoff) paired with a Zigbee2MQTT coordinator never call home — all communication is local. Z-Wave devices through ZWave-JS are the same.
For cameras, Frigate NVR ($0, runs locally) does on-device AI detection using a Coral TPU or even just a decent CPU. Your camera footage processes on your own hardware. Amcrest, Reolink, and many others support RTSP streams that Frigate can ingest directly, with no cloud involved.
I run Frigate on a mini PC with a Coral USB Accelerator ($60). It processes camera streams from four cameras in real time, stores recordings locally on a 4TB drive, and has never sent a frame of footage outside my network.
Step Five: Specific Actions for Specific Devices
Amazon Echo: Go to Alexa Privacy settings, turn off "Use of voice recordings for product improvement." Review and delete voice history. Consider whether you need the Echo always-on at all — a manual trigger (button press) model like a Fire tablet in Kiosk mode is more privacy-preserving.
Google Nest: Turn off Web & App Activity, disable Audio Activity. Set auto-delete for activity data to 3 months.
Smart TV: Disable ACR. On Samsung: Settings > Support > Terms & Conditions > SyncPlus. On LG: Settings > All Settings > General > AI Service > AI Sound Pro. On Vizio: Settings > Reset & Admin > Viewing Data. On Roku: Settings > Privacy > Advertising > Limit Ad Tracking, and disable "Use information from TV inputs" under Channels.
Robot vacuums: Don't link your iRobot to third-party services. Disable the "connected home" data sharing in the iRobot Home app. For maximum control, flash a Roomba with Home Assistant's built-in Roomba integration to avoid the iRobot cloud entirely.
Ring cameras: Disable "Share Content for Feature Improvements" and "Show Ring ads." Know that Control Center > Video Requests shows if law enforcement has requested your footage.
The Tradeoff Is Real
I won't pretend local-first is free. Home Assistant has a learning curve. Running a Pi-hole requires basic Linux comfort. Frigate needs hardware investment.
The tradeoff is convenience versus control. A fully cloud-dependent smart home is easier to set up and maintain. A locally-controlled smart home requires more investment upfront and you're responsible for your own maintenance and updates.
My recommendation: start with network segmentation (do this first, it's the most impact for least effort), then work through the device-specific settings in Step Five. That gets you 80% of the privacy benefit without any new hardware. If you decide you want more control from there, Home Assistant is the path.
The goal isn't to paranoid-proof your home. It's to understand what you've agreed to and make deliberate choices about it. That's all.